
The Platinum APT (Advanced Persistent Threat ) group, which is known for there sophisticated Cyber attacks from but no limit to big tech companies to government officials and now Launches a New Trojan.
T
he infamous group is back, in which they launched a new backdoor trojan called Titanium that has been ship with advance capabilities of taking full control over a target’s PC.Hacking Group Launches A New Trojan.
The Titanium Trojan has the capabilities of hiding in plain sights, such as disgusting itself as a DVD burner software, sound drivers, and evening security software. They are reported by the Kaspersky Lab researchers.
You may also like Top 8 Hacking Techniques
The Platinum APT ground has been active for the past ten years, especially in South and Southeast Asia, infiltrating government institutions, defense institutions, intelligence agencies, and telecommunication companies.
Titanium attacks include a complex sequence of dropping, downloading, and the installation stages of the trojan in which the final step is leaving a backdoor.
Security software evidence of the Titanium trojan uses numerous amount of tricks like encryption, camouflaging as essential drivers, and delivering data stenographic in PNG images.
After a computer has been infected by Titanium trojan, it drops its final payload by downloading the required files using windows B.I.T.S (Background Intelligent Transfer Service). the trojan then starts C2 server communication using the cURL tool.
To establish a connection to the Titanium C2 server it first sends ” a base64-encoded request which contains a hard drive serial number, unique SystemID, and computer name” once those requests been made its starts receiving commands from the attacking group server.
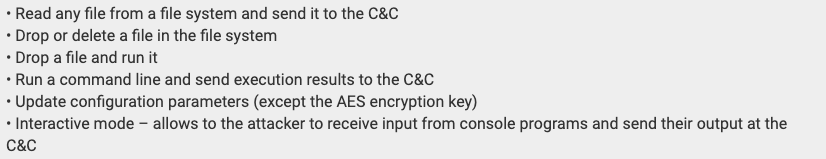
Some of the tasks that the trojan can accomplish are:
Kaspersky researchers say that it has not detected any activity related to Titanium trojan. But, it could be out there since it is tough to identify the backdoor owing to its fileless technology and encryption techniques.